This howto assumes you already have ssh access to your server which is otherwise outside of the scope of this discussion.
When you setup your first Vircadia server in Ubuntu there are no firewall rules enacted. Security is up to you. This is necessary to protect your Vircadia server from agents who have ill intentions toward your environment. I will explain to you how to quickly setup your firewall rules in Ubuntu. The ports required by Vircadia are described in the documentation.
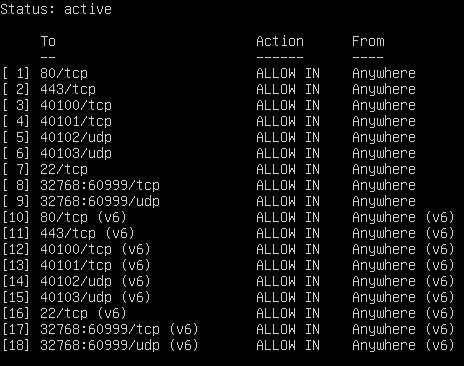
Namely you have the following ports:
- 40100 (+0): (tcp) administrative http connection
- 40101 (+1): (tcp) administrative https (encrypted) connection
- 40102 (+2): (udp) main connection from clients
- 40103 (+3): (udp) main connection from clients (encrypted)
I am adding port 80 (html) and 443 (secure html) so that you will be able to reach out and in through standard internet protocols. Those ports are optional. We will also add port 22 to allow ssh to continue working.
EDIT: I am adding the ephemeral ports 32768-60999 for all the additional servers and mixers. You can read about this in the comments below. Thank you @madders for pointing this out.
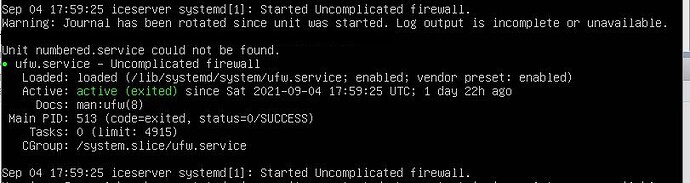
The most basic firewall which comes standard on Ubuntu 18.04 is UFW (Uncomplicated Firewall). If you are using a standard Ubuntu installation then it is already installed and running. It however has NO rules enabled. This basically means your server is wide open for attacks of various kinds. Let’s remedy this security hole right now.
SSH into your Vircadia server and type the following:
sudo ufw status numbered
When you use the ‘numbered’ tag it will list all rules setup by number… if however you have no rules it will look something like this.
Fist there are no numbered rules (the first hint it isn’t configured) and second you can tell it is running and enabled. Let’s setup our rules.
From your ssh prompt type in and enter the following lines, one by one.
sudo ufw disable
sudo ufw default deny incoming
sudo ufw default allow outgoing
sudo ufw allow 22/tcp
sudo ufw allow 40100/tcp
sudo ufw allow 40101/tcp
sudo ufw allow 40102/udp
sudo ufw allow 40103/udp
sudo ufw allow 32768:60999/tcp
sudo ufw allow 32768:60999/udp
sudo ufw allow 80/tcp
sudo ufw allow 443/tcp
sudo ufw enable
The first command ensures that UFW is disabled while you setup the commands, otherwise you will get locked out before you setup port 22 for ssh access.
The next two lines do the heavy lifting of protecting your system. They basically deny everything except outgoing requests so you will have to tell it what ports are safe by enabling them.
The remaining lines up to the last one will open access to the ports we want open to visitors and ourselves.
The last command enables, activates UFW and ensures your ports are open as desired. You can choose to use different ports but that is outside the scope of this howto… please feel free to ask questions. Run the following command to see your configuration:
sudo ufw status numbered
Your output should look something like this: